Urgent Alert for Miami: Unpatchable Apple Silicon Security Flaw Exposes Data
Table of Contents
- Introduction: Urgent Alert for Miami
- The Flaw Unveiled
- Implications for Users and Businesses
- Navigating the Threat Landscape
- Prime Tech Support: Pioneering Digital Security Solutions
- Customized Security Workshops
- Proactive Monitoring and Response
- Community Engagement: Building a Safer Digital Miami
- Conclusion: Join Us in Securing Your Digital Future
FAQs on Apple Silicon Security Flaw
FAQ Table of Contents
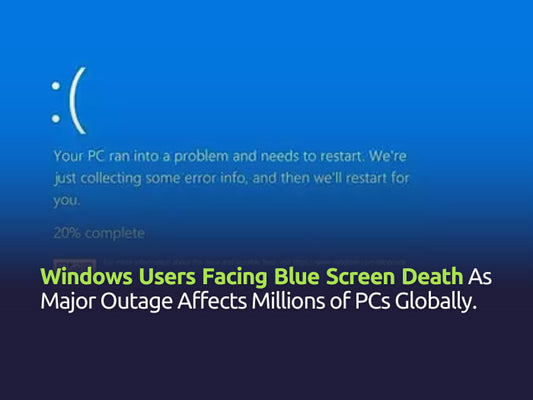
Introduction: Urgent Alert for Miami
shadow over the reliability of some of the most trusted technology in our homes and offices. Researchers have unearthed a significant security flaw within Apple Silicon processors—found in the heart of the latest MacBooks and other Apple devices—that poses an unprecedented risk to data security. This flaw, due to its fundamental nature, cannot be remedied by traditional software updates, prompting a reevaluation of digital security practices and solutions. This comprehensive analysis explores the flaw's technical aspects, its potential impacts, and the bespoke solutions offered by Prime Tech Support to navigate this new challenge.
The Flaw Unveiled
The vulnerability at hand affects the Apple M1, M2, and subsequent Silicon processors, integral to the performance and efficiency of Apple's newest devices. Dubbed "GoFetch" by the cybersecurity community, this flaw allows for the extraction of secret encryption keys due to a microarchitectural weakness in the processor's design. These encryption keys are vital for securing data, from personal photos and documents to corporate intellectual property. The article written originally by Arstechnica reporter Dan Goodin explains the technicalities fo th flaw.
Implications for Users and Businesses
The implications of the Apple Silicon security flaw are significant for both individual users and businesses. The vulnerability allows attackers to extract sensitive encryption keys directly from devices, potentially leading to serious data breaches. This risk extends to personal data, potentially enabling identity theft, and to corporate information, which could compromise business operations and security. The nature of this flaw underscores the evolving challenges in digital security, highlighting the necessity for advanced protection measures beyond traditional software updates to safeguard against such sophisticated threats.
Navigating the Threat Landscape
To navigate the landscape of digital threats, particularly unpatchable flaws, a sophisticated defense strategy is essential. Prime Tech Support recommends a multi-layered approach to cybersecurity. This includes employing external encryption to protect data, even if system-level security is compromised.
Furthermore, practicing robust digital hygiene—regularly updating software, using strong, unique passwords, and educating oneself on phishing tactics—forms a critical line of defense. Implementing these measures creates a comprehensive shield against potential breaches, safeguarding personal and business data from sophisticated cyber threats.
Need top-notch MAC support? Discover how our team at Prime Tech Support provides expert MAC technical assistance across Miami. Read more about our services and how we can help you from Miami.
Prime Tech Support: Pioneering Digital Security Solutions
As Miami's Premier IT Support and Digital Security Provider, Prime Tech Support is at the forefront of addressing this critical vulnerability. Our team of experts is equipped with cutting-edge tools and knowledge to implement comprehensive security strategies tailored to the unique needs of each client. From in-depth risk assessments to the deployment of advanced encryption technologies, we ensure that your digital assets are protected against current and future threats.
Through seminars and consultations, we demystify these complex concepts, empowering our clients with the knowledge to make informed decisions about their digital security.
Contact PRIME Tech Support in Miami for your Data Security
Customized Security Workshops
Prime Tech Support's customized security workshops play a crucial role in enhancing digital defenses by educating participants on potential cyber threats and effective countermeasures. Tailored to both individuals and businesses, these sessions are meticulously designed to impart practical skills and knowledge, enabling attendees to identify risks and implement robust security practices.
Through interactive learning experiences, these workshops aim to fortify the digital safety of participants, making them a vital component of a comprehensive cybersecurity strategy.
Proactive Monitoring and Response
In today's interconnected digital landscape, the importance of safeguarding business operations cannot be overstated. Our proactive monitoring and response services are designed to provide peace of mind by continuously overseeing your IT systems and ensuring they are secure from potential threats.
Comprehensive Proactive Monitoring:
At the heart of our approach is a robust proactive monitoring system that vigilantly watches over all aspects of your digital infrastructure. This includes real-time scanning for unusual activity, performance anomalies, and potential security breaches. By implementing cutting-edge technology and sophisticated monitoring tools, we ensure that your network, servers, and applications are always under careful scrutiny.
Key Features of Our Monitoring Services:
- Real-Time Alerts: Immediate notifications about any irregular activity, allowing for quick assessments.
- Performance Benchmarks: Regular checks against performance standards to ensure optimal system operation.
- Customized Reports: Detailed insights into system health and security, tailored to specific business needs.
Rapid Response to Threats:
The moment our monitoring systems detect a potential issue, our rapid response teams are activated. Composed of seasoned IT professionals, these teams are equipped with the necessary tools and knowledge to address and neutralize threats swiftly. Our response protocol includes:
- Immediate Threat Assessment: Evaluating the severity and potential impact of the threat.
- Quick Containment: Implementing measures to prevent the spread of the threat within your infrastructure.
- Resolution and Recovery: Addressing the root cause of the issue and restoring systems to full functionality.
- Post-Incident Analysis: Detailed analysis to prevent future incidents and strengthen security postures.
Benefits of Proactive Monitoring and Response:
- Minimized Downtime: By catching issues early, we significantly reduce the risk of prolonged system failures.
- Enhanced Security: Continuous oversight helps protect against data breaches and cyber-attacks.
- Cost Savings: Preventative measures mean fewer expensive repairs and recovery operations.
- Peace of Mind: Knowing that experts are watching over your systems 24/7 lets you focus on growing your business.
The Road Ahead: Innovations in Digital Security
Looking forward, Prime Tech Support remains committed to pioneering innovative solutions to the ever-evolving challenges of digital security. Our ongoing research and development efforts aim to stay ahead of threats, ensuring that our clients benefit from the most advanced protections available.
Community Engagement: Building a Safer Digital Miami
At Prime Tech Support, our commitment extends beyond providing exceptional IT services. We are deeply invested in building a safer digital environment for the Miami community. Our efforts in community engagement and collaboration with local organizations underline our dedication to enhancing digital security awareness and practices across the city.
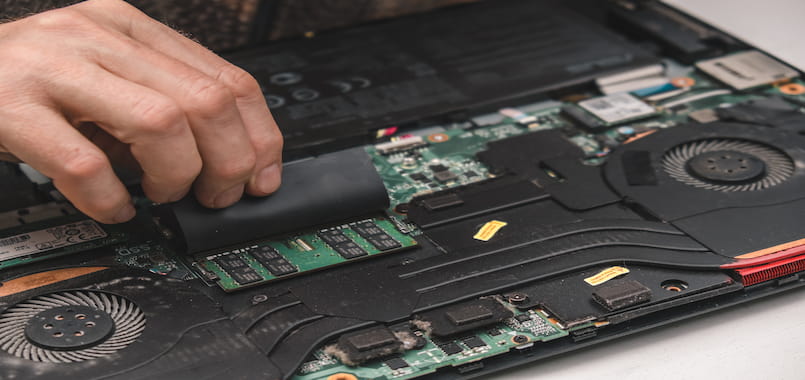
Hands-On Support and Repairs:
We also contribute by offering hands-on support and repairs within the local community. This practical assistance not only helps resolve immediate technological issues but also reinforces the importance of maintaining secure and efficient digital systems. Our team’s presence in the community ensures that help is never far away, promoting a culture of prompt and effective problem-solving.
Raising Awareness through Events and Initiatives:
Each year, we spearhead several initiatives aimed at promoting digital security. From participating in local tech fairs to organizing 'Digital Safety Weeks,' our events are designed to engage the public and provide them with tools and knowledge to protect themselves online.
Active Community Involvement:
Our team at Prime Tech Support doesn't just work behind computers; we're out in the community, meeting people and learning about their IT needs. By hosting workshops, seminars, and information sessions, we empower residents and businesses with the knowledge to safeguard their digital assets effectively.
Conclusion: Join Us in Securing Your Digital Future
In light of the unpatchable Apple Silicon security flaw, the need for vigilant and innovative digital security solutions has never been more apparent. Prime Tech Support invites you to join us in safeguarding your digital assets against this and future vulnerabilities. Contact us today to learn more about our services and how we can assist in fortifying your digital defenses, ensuring peace of mind in an uncertain digital age.
Hire PRIME Tech Support in Miami for Apple Computer Security
How does the Apple Silicon flaw affect my devices?
This flaw could allow unauthorized access to sensitive data on devices with Apple Silicon chips, posing a risk to personal and business information.
What immediate steps should I take?
Users are advised to follow best practices for digital security, stay informed on updates from Apple, and consider additional protective measures like encryption.
How can Miami residents secure their devices?
Miami residents should consider engaging with local tech support services like Prime Tech Support for personalized advice and solutions to mitigate risks from this flaw.
SAME-DAY SERVICE
Miami Tech Support
We service your computers In-Store or in your location. Same-Day IT Support & PC Repairs.